TL;DR
This ransomware explained guide covers what ransomware is, how it spreads, and how to defend against it. Ransomware encrypts data and may also steal it for extortion. Strong cybersecurity practices, such as backups, system updates, and access controls, are essential for effective ransomware prevention and recovery.
Ransomware can be explained as one of the most disruptive cybersecurity threats facing individuals and organizations today. These attacks can shut down businesses, disrupt hospitals, and result in significant financial and reputational damage.
So, what is ransomware? It is a type of malicious software designed to block access to systems or data until a ransom is paid. But modern ransomware attacks go beyond simple file encryption; they often involve data theft, system disruption, and coordinated network attacks.
Understanding ransomware in practical terms helps individuals and organizations not only recognize threats but also implement effective prevention and response strategies.
Ransomware Explained: What Is Ransomware, and How Does It Work?
Ransomware is a form of malware that encrypts files or locks access to systems, preventing users from retrieving their data. Attackers then demand payment, typically in cryptocurrency, in exchange for a decryption key.
Understanding how ransomware works requires looking at the attack lifecycle:
- Initial Access: The attacker gains entry through phishing, vulnerabilities, or stolen credentials
- Execution: The ransomware installs and begins running on the system
- Lateral Movement: It spreads across networks to infect additional devices
- Encryption: Files are encrypted using strong cryptographic algorithms
- Extortion: A ransom note is displayed demanding payment
Modern ransomware attacks often include double extortion, where attackers not only encrypt data but also steal it and threaten to publish it if payment is not made. Many attacks are also delivered through Ransomware-as-a-Service (RaaS), where cybercriminal groups provide ready-made ransomware tools to affiliates, increasing the scale and frequency of attacks.
According to CISA, ransomware is particularly dangerous for organizations that depend heavily on data and operational continuity.
How Does Ransomware Infect Devices or Networks?
What are the most common ways ransomware infects a device or network? Ransomware infections typically exploit either human error or system vulnerabilities.
The most common entry points include:
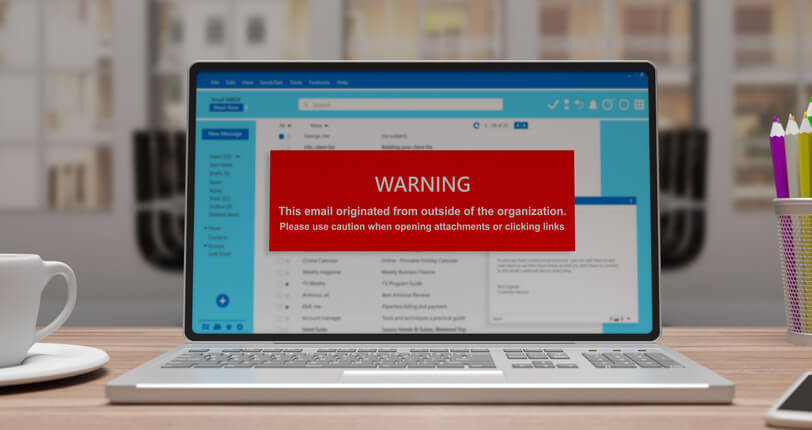
- Phishing emails with malicious links or attachments
- Compromised websites and drive-by downloads
- Unpatched software vulnerabilities
- Unsecured Remote Desktop Protocol (RDP) access
- Weak or stolen credentials
More advanced attacks may involve:
- Malvertising (malicious online ads)
- Supply chain compromises
- Credential dumping and privilege escalation
Once inside a system, ransomware can spread rapidly across networks, targeting shared drives, servers, and backup systems.
Understanding these risks is a key part of modern cybersecurity awareness, often introduced through foundational topics like the anatomy of a breach. If ransomware successfully infiltrates a system, immediate action becomes critical.

What Should You Do If You’re Infected?
What should you do immediately if you think you’re infected? A fast and structured response is critical to limiting damage.
Key steps include:
- Disconnect the affected device from the network immediately
- Disable Wi-Fi, Ethernet, and remote access connections
- Report the incident to IT or cybersecurity professionals
- Preserve logs and evidence for investigation
- Assess the scope of the infection before attempting recovery
Avoid attempting random fixes or deleting files, as this can interfere with recovery efforts. Microsoft recommends isolating affected systems and following a structured incident response plan.
Authorities such as CISA generally advise against paying the ransom, as payment does not guarantee data recovery and may encourage further attacks.
Can You Recover Files Without Paying the Ransom?
Can you recover files without paying the ransom, and what role do backups play? In many cases, ransomware recovery is possible without paying attackers, especially when reliable backups are available.
Effective backup strategies include:
- Offline backups that are disconnected from the network
- Cloud backups with versioning
- Immutable backups that cannot be altered or deleted
Before restoring data, systems must be fully cleaned to ensure the ransomware is removed. Restoring infected systems without proper remediation can lead to reinfection.
Some cybersecurity tools can decrypt certain ransomware variants, but this is not always possible. This is why prevention and preparation are far more reliable than recovery alone.

Ransomware Prevention Strategies
Strong ransomware prevention requires a layered security approach.
Key strategies include:
- Regular software updates and patch management
- Strong password policies and multi-factor authentication (MFA)
- Employee awareness training to detect phishing attempts
- Endpoint Detection and Response (EDR) tools for threat monitoring
- Network segmentation to limit lateral movement
- Least privilege access controls to restrict system access
- Secure and tested backup systems
Adopting structured network security best practices, such as Identity and Access Control Management, helps organizations build resilient defenses that reduce the impact of ransomware attacks.
Why Cybersecurity Skills Matter
As ransomware threats continue to evolve, the demand for cybersecurity professionals is growing rapidly.
Understanding ransomware is just one part of a broader skill set that includes:
- Threat detection and monitoring
- Incident response and recovery
- Digital forensics
- Network and endpoint security
Cybersecurity professionals use tools such as SIEM platforms, threat intelligence systems, and endpoint protection solutions to detect and respond to attacks. Cybersecurity training programs at Cumberland College help students develop the skills needed to protect systems and pursue careers in this high-demand field.
Are you looking for comprehensive cybersecurity courses?
Contact Cumberland College for more information.
Key Takeaways
Ransomware is a serious cybersecurity threat that encrypts and may also steal data for extortion. Understanding what ransomware is and how it works is essential for prevention.
Most attacks occur through phishing, vulnerabilities, or weak access controls. Modern ransomware often includes advanced tactics such as double extortion and network-wide infection.
Strong ransomware prevention strategies, such as backups, access controls, and threat detection, are the most effective defense. With the right knowledge and preparation, individuals and organizations can significantly reduce risk and improve ransomware recovery outcomes.
FAQ
What is ransomware, and how does it work?
Ransomware is malware that encrypts data or locks systems, demanding payment for access. Modern variants may also steal data for extortion.
What are the most common ways ransomware infects a device or network?
Common methods include phishing emails, malicious downloads, unpatched vulnerabilities, and weak remote access security.
What should you do immediately if you think you’re infected?
Disconnect the device from the network, report the incident, preserve evidence, and follow a structured incident response process.
Can you recover files without paying the ransom, and what role do backups play?
Yes. Secure backups allow data restoration without paying attackers and are one of the most effective recovery strategies.