TL;DR
A SOC analyst works inside a Security Operations Centre (SOC) to monitor networks, detect cyber threats, and respond to security incidents. Using SIEM tools, analysts perform continuous security monitoring, investigate suspicious activity, and coordinate incident response to protect organizations from cyberattacks.
Cybersecurity threats are becoming more sophisticated every year. Businesses, governments, and organizations need cybersecurity professionals who can continuously monitor systems and respond quickly to suspicious activity. One of the professionals responsible for detecting and responding to these threats is the Security Operations Center (SOC) analyst.
A Security Operations Center (SOC) is a centralized team responsible for protecting an organization’s IT infrastructure and digital assets. Inside the SOC, analysts monitor networks, investigate alerts, and coordinate incident response when potential threats are detected.
The role of a security analyst in a SOC is both technical and investigative. Analysts must understand network behaviour, identify suspicious patterns, and determine whether an alert represents a real attack or a false alarm.
Students interested in cybersecurity careers often start by learning these skills through structured training programs such as cybersecurity courses.
What Is a SOC Analyst?
A SOC analyst is a cybersecurity professional responsible for monitoring systems, identifying potential threats, and responding to security incidents.
Security Operations Centres function as the frontline defence against cyberattacks. Analysts monitor incoming security data from multiple systems, looking for signs of suspicious activity or abnormal behaviour.
SOC teams play a critical role in identifying, analyzing, and responding to cybersecurity incidents before they escalate. As cyber threats evolve constantly, SOC Analysts must remain vigilant and adaptable while protecting sensitive systems and data. According to the Canadian Centre for Cyber Security, organizations must continuously monitor networks to detect and respond to emerging cyber threats.
What Are the Daily Tasks of a SOC Analyst?
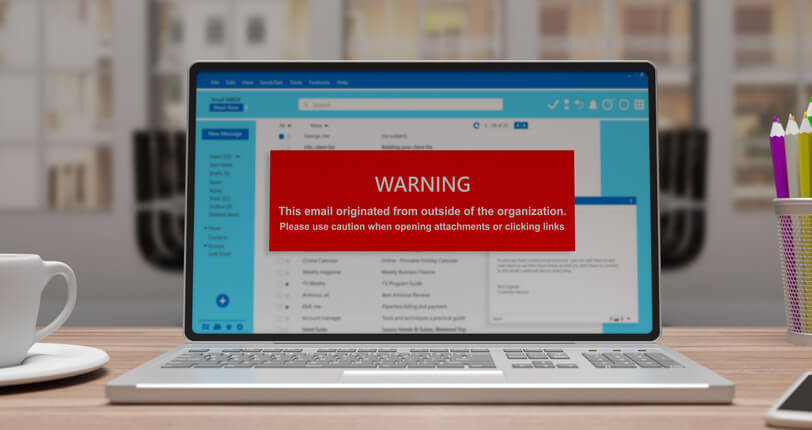
A typical day for a SOC analyst revolves around continuous security monitoring, alert investigation, and incident response. Analysts begin by reviewing alerts generated by monitoring systems. These alerts might indicate unusual log-in activity, network anomalies, malware behaviour, or suspicious file transfers.
When an alert appears, analysts investigate the activity to determine whether it represents legitimate behaviour or a possible attack. If the activity appears malicious, they escalate the issue and initiate incident response procedures.
Other responsibilities include documenting incidents, reviewing security logs, and updating detection rules to improve threat detection accuracy. Analysts may also collaborate with other security professionals to investigate complex cyber incidents. This work requires strong analytical thinking and strong attention to detail.
What Tools Do SOC Analysts Use?
One of the most important technologies used in modern security operations is the Security Information and Event Management system, commonly known as SIEM tools.
SIEM platforms aggregate, normalize, and correlate logs from multiple systems to identify suspicious activity across an organization’s infrastructure. These may include servers, firewalls, endpoint devices, cloud systems, and applications.
By aggregating this data, SIEM systems help analysts identify patterns that could indicate cyberattacks. For example, a SIEM platform might detect repeated login failures, unusual network traffic, or unauthorized access attempts.
These tools allow security teams to correlate events across multiple systems and detect complex threats faster. Other tools commonly used by SOC analysts include threat intelligence platforms, endpoint detection systems, vulnerability scanners, and forensic analysis software.
Learn how to get into cybersecurity with zero experience? We explain how in this blog post.
What Skills Do SOC Analysts Need?
Successful security analysts combine technical expertise with analytical problem-solving.
One of the most important skills is understanding network behaviour and identifying anomalies that could signal cyber threats. Analysts also need familiarity with operating systems, networking protocols, and cybersecurity frameworks.
Communication skills are equally important. SOC analysts often document incidents and explain findings to other technical teams or management.
The ability to respond quickly during security incidents. Effective incident response requires analysts to analyze data, identify attack patterns, and recommend containment actions.
Training programs help students build these skills while learning about modern cybersecurity tools and defensive strategies.

Why SOC Analysts Are Essential to Cybersecurity
Organizations rely on SOC teams to protect sensitive data and critical infrastructure.
Without continuous security monitoring, cyberattacks could remain undetected for long periods. A skilled SOC analyst helps detect threats early and prevent them from escalating into major security breaches.
As cyber threats grow more complex, the demand for trained security professionals continues to increase. Many organizations actively recruit analysts who understand threat detection, monitoring tools, and incident investigation.
For students exploring cybersecurity careers, SOC analyst roles often serve as an entry point into the broader field of cybersecurity operations.
Are you looking for comprehensive cybersecurity courses?
Contact Cumberland College for more information.
Key Takeaways
A SOC analyst monitors systems, investigates alerts, and responds to cyber threats inside a Security Operations Centre.
Using SIEM tools and other cybersecurity platforms, analysts perform continuous security monitoring and support incident response when suspicious activity appears.
Because cyber threats are constantly evolving, organizations rely heavily on skilled security professionals who can detect and respond to attacks quickly.
For individuals interested in cybersecurity careers, developing these skills through professional cybersecurity courses can be an important first step toward entering the field.
FAQ
What tools do SOC analysts use?
SOC analysts commonly use SIEM tools, endpoint detection platforms, threat intelligence systems, and network monitoring software.
What are the daily tasks of a SOC Analyst?
A typical day for a SOC analyst revolves around continuous security monitoring, alert investigation, and incident response.
What skills do SOC analysts need?
SOC analysts need networking knowledge, cybersecurity fundamentals, analytical thinking, and strong communication skills for incident investigation and reporting.